In cryptography, a plaintext message is converted to ciphertext when using a technique, or a combination of numerical computations, that appear incomprehensible to the untrained eye. Let’s say there is a smart guy called Eaves who secretly got access to your communication channel. Since this guy has access to your communication, he can do much more than just eavesdropping, for example, he can try to change the message. Cryptography is used in e-commerce transactions to encrypt sensitive data, such as credit card information, during transmission to ensure its confidentiality and integrity. Other forms of cybersecurity focus on other fronts such as protecting the network, limiting or stopping access to data, and protecting data from manipulation, i.e. deliberate corruption of meaning or readability.
The number of keys required increases as the square of the number of network members, which very quickly requires complex key management schemes to keep them all consistent and secret. Cryptosystems use a set of procedures known as cryptographic algorithms, or ciphers, to encrypt and decrypt messages to secure communications among computer systems, devices and applications. Symmetric-key cryptographic algorithms use the same cryptographic keys for both the encryption of the plaintext and the decryption of the ciphertext. Symmetric encryption requires that all intended message recipients have access to a shared key. A cryptographic algorithm is a math-based process for encoding text and making it unreadable.
Internationally agreed ways of working make technology more secure and interoperable. By using cryptography standards, developers can rely on common definitions, as well as proven methods and techniques. Unlike today’s computer systems, quantum computing uses quantum bits (qubits) that can represent both 0s and 1s, and therefore perform two calculations at once. While a large-scale quantum computer may not be built in the next decade, the existing infrastructure requires standardization of publicly known and understood algorithms that offer a secure approach, according to NIST.

In a safe cryptographic system, even though you know the process by which a particular message is encrypted, it must be hard or impossible to decrypt without that key. Additionally, Gmail data is secured using cryptography and is transmitted throughout Google data centers in an encrypted manner. Cryptography is therefore regarded as the essential what Is cryptography component for protecting shared information. Moving keys between systems should only occur when the key is encrypted or wrapped under an asymmetric or symmetric pre-shared transport key. If this is not possible, then the key must be split up into multiple parts that are kept separate, re-entered into the target system, then destroyed.
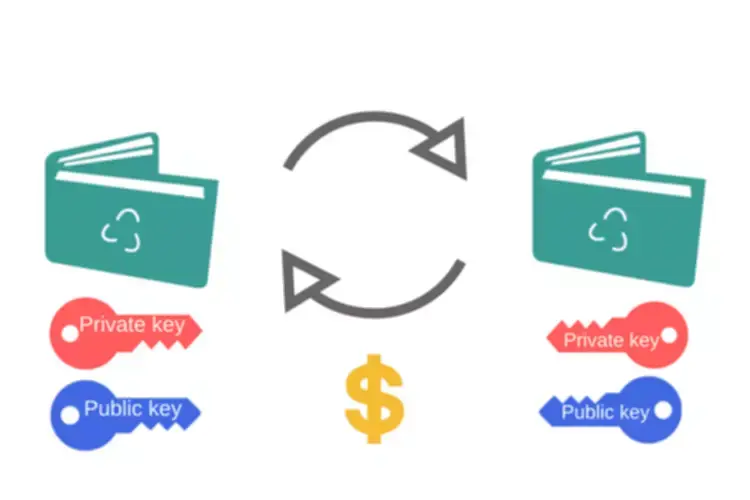
Cryptography also secures browsing, such as with virtual private networks (VPNs), which use encrypted tunnels, asymmetric encryption, and public and private shared keys. A common cryptography definition is the practice of coding information to ensure only the person that a message was written for can read and process the information. This cybersecurity practice, also known as cryptology, combines various disciplines like computer science, engineering, and mathematics to create complex codes that hide the true meaning of a message. Hash functions have many applications in computer science and information security, including cryptography, data integrity checking, data indexing, data fingerprinting, password storage, digital forensics, and blockchain. Both forms are considered secure, but the level of security in any given encrypted message has more to do with the size of the key(s) than the form of encryption. Just like passwords, keys must be complex, difficult to obtain, decode, or reveal.
Hashing is the process of taking a key and mapping it to a specific value, which is the hash or hash value. A hash function transforms a key or digital signature, then the hash value and signature are sent to the receiver, who uses the hash function to generate the hash value and compare it with the one they received in the message. IBE is a PKC system https://www.xcritical.in/ that enables the public key to be calculated from unique information based on the user’s identity, such as their email address. A trusted third party or private key generator then uses a cryptographic algorithm to calculate a corresponding private key. This enables users to create their own private keys without worrying about distributing public keys.
Also, public keys are usually linked to identities by organizations known as Certificate Authorities. Samuel wishes to communicate with his colleague Yary, who is currently residing in another country. The message contains trade secrets that should not be accessed or seen by any third party.
If the codes match, it means the data stayed safe during transmission and storage. Whether you’d like to gain knowledge on cybersecurity for your personal use or your new career, you can sign up for a beginner lesson to provide you with a fundamental insight into the prevailing scene of data security. There are two types of cryptography attacks, passive and active attacks. A language is used to hide the meaning of the sentences written in a different language.
These primitives provide fundamental properties, which are used to develop more complex tools called cryptosystems or cryptographic protocols, which guarantee one or more high-level security properties. Note, however, that the distinction between cryptographic primitives and cryptosystems, is quite arbitrary; for example, the RSA algorithm is sometimes considered a cryptosystem, and sometimes a primitive. Typical examples of cryptographic primitives include pseudorandom functions, one-way functions, etc. Currently used cryptography techniques can potentially be irreversible, ensuring the message’s security forever. The requirement for data to be safeguarded more securely than ever before has led to the development of more complex cryptography methods. Most early cryptographic ciphers and algorithms have been cracked, making them ineffective for data security.
- While symmetric encryption requires the sender and recipient to use the same key, that key’s use is not limited to two people in a linear conversation.
- It is an essential line of defense in cybersecurity architecture and hinders an attacker’s efforts to access sensitive information.
- Almost all passwords are stored securely as hashed functions which are then used to verify the correct password is being used.
To safeguard your information and data shared over the internet it is important to use strong encryption algorithms, to avoid any catastrophic situations. The encryption process where different keys are used for encrypting and decrypting the information. Keys are different but are mathematically related, such that retrieving the plain text by decrypting ciphertext is feasible. After using the key for decryption what will come out is the original plaintext message, is an error. It is the way Sam knows that message sent by Andy is not the same as the message that he received.
The Caesar cipher we discussed above is a great example of symmetric cryptography. But the key needs to stay a secret between the two of them, which is why this is sometimes also called secret key cryptography. You couldn’t send the key along with the message, for instance, because if both fell into enemy hands the message would be easy for them to decipher, defeating the whole purpose of encrypting it in the first place. Caesar and his centurion would presumably have to discuss the key when they saw each other in person, though obviously this is less than ideal when wars are being fought over long distances.
This is most likely to occur through a rogue employee having access to a key, then using it for malicious purposes or giving or selling it to a hacker or third party.
Another potential solution is cryptography quantum, whereby it is impossible to copy data encoded in a quantum state. Every key should only be generated for a specific single-use encrypt/decrypt purpose, and use beyond that may not offer the level of protection required. Having a solid foundation in cryptography basics allows us to secure our confidential data. The intruder will try to gain as much access to the computer system as possible. Masquerade is an active attack that threatens the security goal of credibility. The RSA algorithm has the drawback of being quite inefficient in cases in which large volumes of data must be authenticated by the same virtual machine.